Introduction
When I first heard the news, my first thought was – how can a hacker group breach so many systems across so many government agencies so quickly? My answer was simple: they cannot. The inevitable conclusion is that they have infiltrated the government systems for months, if not years, waiting for the time they decided to strike.
There must be a systemic problem if someone compromised so many systems across multiple government agencies over a long time. That is not a flaw in one system, a single network, or even one agency – it is a problem across the board. It means there is a fundamental flaw in our security strategy.
Hackers can breach our perimeters and roam inside our systems for a long time, and we’ll have no idea. That is the reality we have just witnessed.
The Problem
That is not the first time we’ve seen hackers infiltrate organizations for months and years. Most large data breaches manifest over a long time.
That is not the first time we’ve seen hackers infiltrate organizations for months and years. Most large data breaches manifest over a long time.
However, we could always find some excuse – they failed to patch this, upgrade that, install an antivirus, etc. There’s always a reason we hang on to, hoping to learn and do better.
But maybe it’s time to accept that the problem is our fundamental approach to security. That the way we do security isn’t working against the existing threats.
Because the simple fact is that the perimeter will always be breached sooner or later, and once the hackers are in – we are clueless. We don’t know they got in, what they’re doing, or how long they’re doing it for.
The Laundry List
The challenge in cybersecurity is that it spans many disparate domains, and we tend to get bogged down by the details of each, losing the view of the bigger picture.
Before looking at methodologies, we should start with a short overview of these different efforts. After all, any strategy will have to include these somehow.
- Network security – some interpret this differently, but here we mean protecting the corporate network from the internet and isolating internal segments from one another. Network security involves firewalls, routers, VPNs, etc.
- Endpoint security – relates to desktop and laptop protection. It involves antivirus, anti-malware, and local firewalls. Occasionally, it extends to disk encryption, USB protection, and more. It may also encompass other devices, BYOD, etc.
- Server security – like endpoints, we must also secure the servers. For Windows servers, this is similar to endpoint security. However, server security extends to a wide range of operating systems such as Linux and other Unix variants. It also focuses more on remote management and the services provided by the servers.
- Email security – is a significant security problem. It involves email software, spam filters, and various means of protecting the mail system and its users.
- Vulnerabilities & Patching – known vulnerabilities are often considered a prominent threat. Detecting those and ensuring timely patching helps reduce this exposure.
- Core IT services – standard services managed by the IT department like the Domain Name System (DNS), the Windows Domain Controller (DC), File servers, and more.
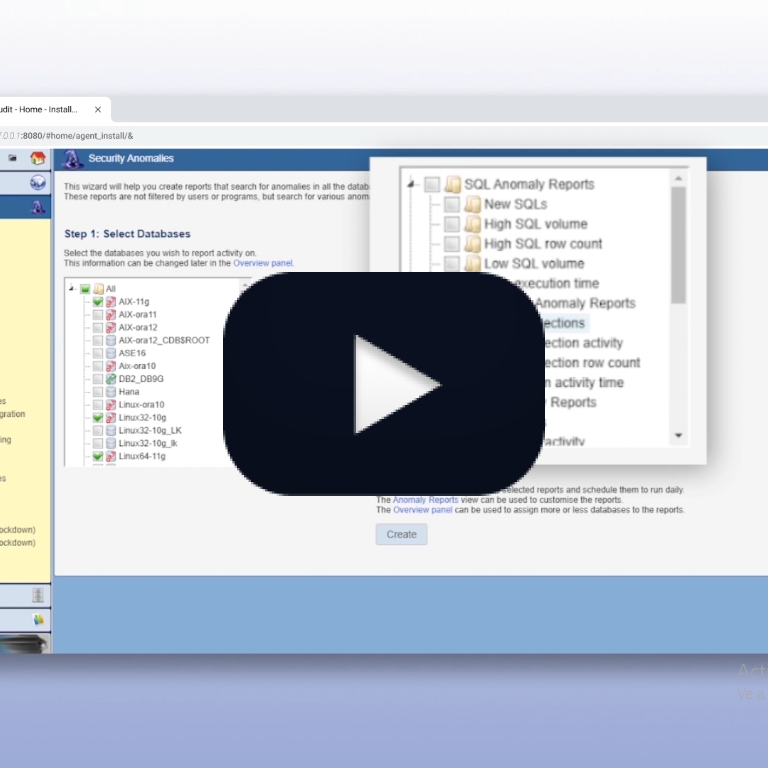
- Application security – protecting in-house and off-the-shelf applications involves a variety of measures relating to quality control, application features (like authentication, authorization, and auditing), and certain products (like WAF and Core Audit).
- Database security – protecting databases includes built-in measures (like users & privileges), processes (like change control), and capabilities like activity auditing.
- Personnel – the Achilles heel of any security strategy. Measures include training, education, and more.
- Security administration – ensuring we know who everyone is and that they have the correct permissions is a challenge in itself. It usually falls into the realm of Identity Access Management (IAM).
- Log management – collecting, analyzing, and correlating logs. It is the realm of Security Information Event Management (SIEM).
Security Methodologies
When examining this long laundry list, it’s hard to notice it contains two distinct security methodologies – Perimeter security and Data-centric security.
Data-centric security is a methodology that revolves around the data. Our objective in cybersecurity is to protect the data, and some of the security measures above are aimed directly at doing that. Data-centric security starts with the database where the data is stored, extending outward to the applications that process that data.
Data-centric security includes database security, application security, and IAM. If these security measures are perfect, we will not have a data breach regardless of how many people breach the firewall. Cloud-based applications, for example, rely entirely on these types of measures.
Perimeter security, on the other hand, aims to prevent attackers from getting in. Preventing them from gaining access to internal systems through which they could access the application or the database. A compromised desktop, in itself, is not a data breach. The data breach would occur if the attacker could navigate from that desktop to the database.
Strategically, there are several important attributes when comparing these methodologies:
- Relevant threats. Perimeter measures are only designed for external threats and are ineffective against internal ones. Threats already inside the perimeter are not addressed. Data-centric security can address both internal and external threats.
- Effectiveness. Perimeter protections are, usually, statistical defenses – they reduce the number of penetrations but don’t prevent them altogether. No matter how good our spam filters, we still get spam emails. No matter how good our personnel training, people still click on spam emails.
Data-centric defenses aim to be as close to 100% as possible. It is the last line of defense and aims to be air-tight. A database security measure that prevents 30% of database attacks is considered worthless. The same applies to application security which will only block 40% of the application attacks. - Compound effect. Perimeter security is a parallel defense. Attackers only need to breach one of the perimeter measures to get in. If attackers fail to penetrate the firewall they can try the mail system, social engineering, compromising an endpoint, etc.
Data-centric security is a serial defense. Attackers must penetrate all the layers. An application breach that fails to execute an attack against the database means a failed attack. Accessing the application using a compromised account still means the attacker needs to run the attack through the application and the database.
Landscape Considerations
When building a security strategy, we must consider the threats we perceive as relevant. For example, are we worried about external threats, internal threats, or both? If internal threats are a significant concern, perimeter security will not be effective against those.
We must also consider the effectiveness of different measures in the current landscape. For example, as more and more people work remotely, network security and endpoint security are less effective. Once people work from home, they are outside the corporate firewall and use their home computers. We have minimal ability to control and secure all these remote mini-offices that bypass the perimeter defense through VPN connections.
BYOD (Bring-Your-Own-Device) poses a similar challenge where many uncontrolled and insecure phones and tablets roam the corporate network.
As the modern landscape changes and the effectiveness of perimeter controls diminishes, there’s a growing need to shift the focus to internal defenses. As part of this shift, there’s a redefinition of the perimeter line – protecting the data center network is becoming as important, if not more, than the corporate network.
Layered Security
Security isn’t always about the weakest link. This soundbite is somewhat true when talking about perimeter defenses deployed in parallel. Attackers that are equally talented at all forms of attack are likely to attack through the weakest link. In this case, the priority is reinforcing the weak link.
However, data-centric defenses deployed in serial can reinforce one another. For example, exploiting a compromised application account could be detected through application auditing or database auditing.
In addition, data-centric measures are always in serial to perimeter defenses and will reinforce weak links in them. No perimeter breach can manifest into a data breach without compromising the internal data management systems.
A strategic layering of defenses can force attacks through many barriers providing powerful protection. Implementation is simple – follow possible attack scenarios and ensure you have different measures at various points along each path.
For example, data-centric philosophy says all attacks must, eventually, penetrate the database. Database protection is, therefore, a high priority, and will reinforce all other defenses.
IDS and IPS
IPS (Intrusion Prevention Systems) aims to prevent attacks and breaches. These are classic security measures like firewalls and passwords.
IDS (Intrusion Detection Systems) aim to detect attacks and report or alert about them. These include measures like auditing and SIEM.
Compared to physical bank security, IPS is like the vault door, while IDS is the alarm system, motion sensors, etc.
For example, we know our IPS systems are under constant attack, but we are never informed about attacks that go through. an IDS informs security personnel of the attack allowing them to respond in different ways. Responses can include taking systems offline, diverting attacks to honeypots, tracing the attack back to its source, and more. In all cases, attackers don’t get a second chance to try and breach the same defense again. IDS systems are, therefore, much harder for attackers to circumvent.
Generally speaking, while IPS could prevent an intrusion, IDS is more likely to detect it and less likely to be circumvented. Therefore, whenever possible, it is always recommended to deploy both types of systems. IPS to block most attacks and IDS to detect the ones that go through.
Strategically, there are important differences between IPS and IDS that are vital to remember:
- Tolerance to false positives. False positives in IPS mean the system prevents users from performing legitimate activities. Therefore, IPS cannot tolerate false positives.
False positives in IDS mean more reports or alerts that require investigation by security personnel. While we don’t want too many false positives in reports and alerts, IDS are designed and calibrated to have a certain amount of those.
Since it’s impossible to perfectly calibrate a security system, zero false positives mean some attacks go through (a false negative). - Response time. IPS must determine whether activities are valid before letting them through. A slow IPS system means a slow response to the protected IT system and users that complain. IPS are, therefore, designed to use real-time algorithms capable of making instant judgment calls.
IDS, on the other hand, can take their time to report or alert. IDS tends to employ more complex algorithms and can analyze large volumes of data to identify intrusions. They can refer to historical information as well as wait for future events to occur and correlate. - Circumvention. When an IPS system prevents an attack, the attacker is, inevitably, aware of the failed attempt and can try again. IPS are, therefore, constantly challenged until being successfully circumvented.
IDS systems don’t inform the attacker and are, therefore, much more difficult to circumvent.
Compensating Activities
When securing a bank vault, you could deploy motion sensors, laser beams, heat sensors, and more. Each type of security measure adds protection and compensates for the limitations of another.
The same principle applies to IT security – doing different activities will increase the likelihood of detecting and stopping a breach.
For example, consider these types of IDS-related activities:
- Declarative auditing. In this form of security monitoring, the security team defines the activity it wishes to monitor. These are usually activities that are high-risk and low-volume.
- Anomaly analysis. In this form of security monitoring, automation built into the security system attempts to detect unusual activity.
- Proactive forensics. In this form of security monitoring, the security team uses tools to investigate and analyze all the activity in the system. The objective is to detect malicious behavior, poor practices, design security controls, and more.
Security Strategy
Finally, we need to design the overall security strategy and determine how to allocate our budget and personnel.
A strategy that maximizes the return on investment and minimizes the chances of a breach should include:
- Balanced methodologies. Balance the strength of perimeter and data-centric defenses. We tend to over-emphasize the importance of perimeter security. The result is that any perimeter breach ends up with a data breach. Perimeter breaches are inevitable and without a solid data-centric posture, we are merely waiting for the breach to occur.
- Balanced perimeter. Balance the strength of the various perimeter measures relative to the risk. A good firewall with no antivirus or spam filter is usually not the best investment unless personnel poses a low risk compared with a network breach.
- Layered security. We cannot overstate the importance of implementing multiple Data-Centric defense layers. It is one of the most effective yet disregarded areas in cybersecurity.
- IPS and IDS. Deploy both IPS and IDS whenever possible. It is vital to know when an IPS is breached and a good IDS is the only way that can happen. It is also a way of adding additional security layers as separate IPS and IDS create two sequential protection barriers.
- Compensating activities. Create as many independent types of activities within each security layer. Different kinds of activities tend to compensate for one another and provide better visibility into what’s going on inside your IT systems.
Final thoughts
Ultimately, security is about visibility. Lack of visibility is how attackers get into your IT systems and roam around for months and years without being detected.
If you don’t feel you know who’s accessing your systems and what’s happening inside them – you are not secured.
Adding multiple protections across multiple systems in a data-centric fashion is also an excellent way to increase visibility into any potential data breach.
But remember that visibility means that security personnel is actively looking at and understanding what’s going on. That means people, time, and appropriate skills. Security done by machines alone is always limited and will be breached sooner rather than later.
Cybersecurity is about constantly improving since we can always do better. Following these concepts to structure a balanced and versatile security strategy will facilitate efficient use of resources while improving your overall security posture. That’s how we can lower the risk of a data breach.
Based in Aliso Viejo, California, Blue Core Research provides advanced security and compliance solutions for databases and applications.
To learn more about data-centric security in general or our solutions in particular, contact us at marketing@bluecoreresearch.com